Access Control: Why should you invest in this technology?
July 10, 2019Concerns about the security and privacy of information are increasingly common, for example in businesses, homes, hotels and local accommodation. Having an access control system that allows the effective and integrated management of buildings is a strategic step for those who want to ensure the security of people, facilities, equipment and sensitive data.
In this article, SEGURTEC explains everything you need to know about access control.
Access control: what is it?
Access control can be defined as the set of subsystems that allow the management of a building, controlling its users, being able to limit its access to certain places and according to a certain schedule, thus recording the movements made by each person, for example.
Thus, the access control system is extremely requested in companies, hotels and residential buildings since it allows supervising the entrance of authorized people and also supervising, for example, which is the last individual to enter and/or leave and the time spent in a certain room.
Access Control: How it’s done
There are numerous technologies available for identification, authorization and/or authentication of people. Among the most common are:
Chip
It uses cards that have a chip inserted, connected to accessible metallic contact points to allow a suitable reader to read the data recorded on that chip.
Contact
Uses devices (usually key rings) that have a chip inserted in a metal capsule. This looks like a large clock stack, which is why they are usually called “iButtom”. When contacting the reader, the devices allow the reading of the data recorded on the chip.
It should be noted that the number on the chip of each identification device is unique and is already recorded at the factory, thus avoiding its duplication or fraud attempts.
Proximity (Contactless)
This method uses devices (usually cards or key rings) with an inserted chip that allows the reading of the recorded data by approaching a suitable reader.
Biometrics
ecurity technology based on the recognition of a physical and non-transferable characteristic of people, such as the fingerprint. This is one of the most credible systems and, therefore, one of the most used when it comes to access control.
Bluetooth
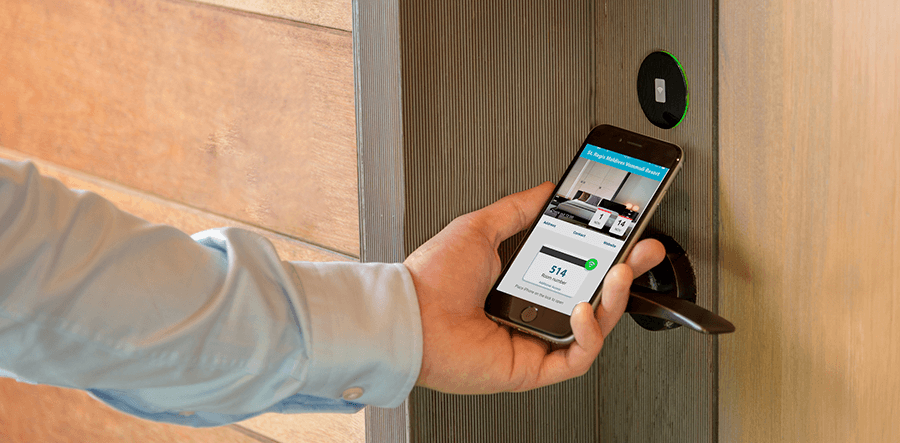
This is a system that uses the mobile phone as an identifier, since each terminal with Bluetooth has a unique code. Therefore, the equipment recognizes the user, allowing (or not) the access. It is a method widely used in hotels and local accommodation to control access to rooms.
Once described some of the main methods of authentication and identification, it is now time to emphasize the equipment used to restrict access. In fact, this is done through physical barriers, namely:
Controllers
They are devices that can make the decision about a user’s access.
Reading terminals
They are equipment only for reading user identifiers, such as reading license plates (especially relevant for the control of entries and exits in enterprises).
Controlled devices
Devices that allow access to or restriction of the enclosure under control by opening or closing it. Examples of controlled devices are locks (door control); barriers (vehicle control); turnstiles (people control); electric foreheads and locks (for door and gate control).
Access Control: Where it can be used
Access Control systems can be used in places such as industrial buildings, car parks, warehouses, residences, hotels and local accommodation establishments and all solutions must be in accordance with the standards in force, guaranteeing all legal requirements and the privacy of the people under surveillance.
Access Control: How SEGURTEC can help you
At SEGURTEC you will find a team with a vast experience and a high knowledge of Access Control solutions. We move by the desire to provide the best services in the market, creating unique and personalized projects. All SEGURTEC’s solutions integrate a maintenance and support service with a demanding and optimised SLA – Service Level Agreement – to guarantee a total reliability and quality in all of the services provided.
See our portfolio , contact us through this form , by email geral@segurtec.pt or by the number (+351) 253 578 161.
We are at your disposal.


